How Identity Cloud works
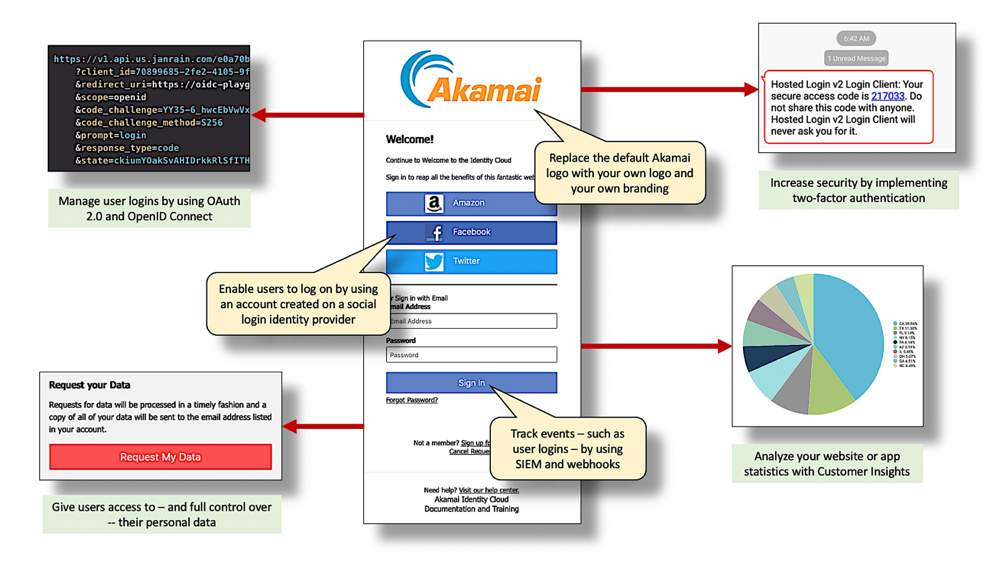
If you read articles about the Akamai Identity Cloud, you’re likely to read that Identity Cloud “reduces user engagement friction” and “empowers users through consent and compliance” and even provides “scoped access control and data analytics and integration.” And all that’s true: Identity Cloud really does reduce user engagement friction. And that's a good thing: whatever user friction is, we probably don’t want any part of it. But that still leaves us with at least one unanswered question: what exactly does Identity Cloud actually do?
Well, as a Customer Information and Access Management (CIAM) product, Identity’s Cloud primary job is to allow users to create accounts on your app or your website, and then be able to return to that website or app and log on to their account. In other words, what Identity Cloud does is display sign-in screens similar to this one:

Admittedly, displaying a sign-in screen doesn’t necessarily qualify as a programming tour-de-force: you could easily write your own code for displaying such a screen. But here’s the deal: would that homemade login and registration system be able to do all the other things that Identity Cloud does for you? Things like:
- Leverage widely-used and widely-accepted standards such as OAuth 2.0 and OpenID connect to help ensure that the login and registration process is safe and secure.
- Enable users to log on to your site using Facebook, Twitter, or practically any other social login identity provider .
- Provide additional security features such as two-factor authentication .
- Give you considerable control over the look and feel of the login and registration experience.
- Make it easy for users to access and manage their accounts and their personal data .
- Provide ways to monitor activity on your website or app, giving you a chance to spot – and to stop – anomalous situations (e.g., malicious activity of some kind) before they become full-blown problems.
- Enable you to view detailed reports regarding your websites, and who (and when, and from where) is actually using those sites.
- Share data with other software, such as a Customer Relations Manager tool .
In this article, we examine these areas in more detail, and provide links to documentation that explains what these features do and what you need to do to implement them. (Hint: in many cases, you don’t have to do much of anything.)
Manage user logins and registrations
At heart, this is what Identity Cloud is all about: enabling users to create accounts in your app or on your website, log on to those accounts, and be recognized as a specific user (e.g., karim.nafir@mail.com) and have access to everything karim.nafir@mail.com is entitled to access. To help manage logins and registrations Identity Cloud’s Hosted Login feature makes liberal use of both OAuth and OpenID Connect, offering support for such things as different grant types, different responses types and modes, and a wide-range of scopes and claims (including custom claims):
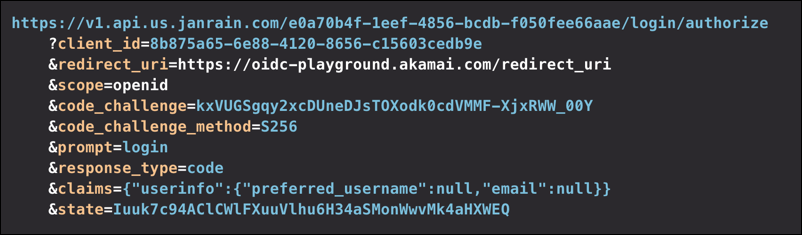
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription.
Do you have to use this feature? Yes. Identity Cloud is built around user logins and registrations: if you don’t use Identity Cloud to log in and register users then none of the other Identity Cloud features (such as Webhooks v3, which can send you a notification each time a user logs on or registers) would have anything to do.
Recommended reading: Introduction to Hosted Login; Introduction to Hosted Login v2; Hosted Login Getting Started Guide
Enable users to use social login
The thought of having to create yet another user account, and having to memorize yet another user account password, might be too much for some people. But that’s OK: after all, Identity Cloud lets users register and to log on with an account created on a social login identity provider such as Facebook, Twitter, or Amazon. That way, there’s no need to worry about a new username or a new password: as long as you can remember how to log on to Facebook you’ll be fine:
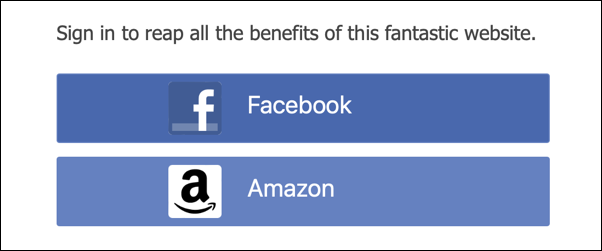
And here’s an added bonus: depending on the identity provider, you can also have data from the social login account automatically copied to the new user’s Identity Cloud user profile. Has the user already entered their address, birthday, and phone number into their Facebook account? Great: that data can (with the proper configuration, and with the user’s explicit consent) be copied to their Identity Cloud account.
Incidentally, out of the box Identity Cloud supports 30 or so social login identity providers. But what if they don’t happen to support the identity provider you want to use? No problem: as long as that provider uses OAuth 2.0, OpenID Connect, or SAML 2 you can employ our custom provider capability to connect to that social login identity provider.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription.
Do you have to use this feature? No; in fact, toggling one configuration setting enables you to turn social login on and off any time you want:
Recommended reading: Configure social login; Configure social login in Hosted Login
Overview video: Configure social login (video)
Add additional security measures
Because Identity Cloud has never experienced a major security breach, you can argue that the product is pretty safe and pretty secure. Still, in this day and age it never hurts to be even safer and even more secure. With that in mind, you can easily implement additional security measures to help protect user accounts. For example, you can implement two-factor authentication to thwart hackers who have somehow acquired a user’s username and password:
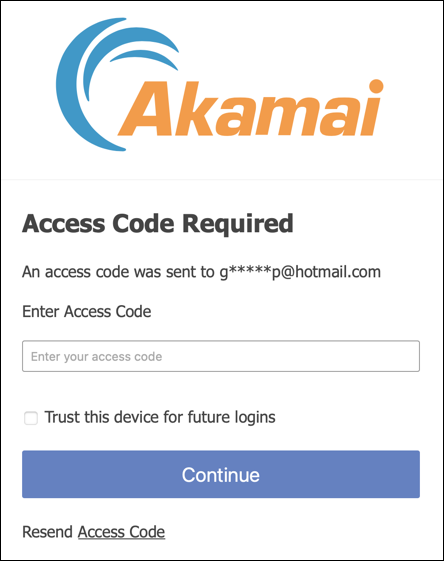
Having the password is of little use if you don’t have the single-use, limited-lifetime access code as well.
In addition to that, you can implement password complexity requirements that prevent users from employing passwords such as password or 123456. You can also enable unique password enforcement, which ensures that a user can’t “change” their existing password to the very same password they’re currently using (The feature can be configured to keep track of the user’s last 10 passwords.)
And speaking of passwords, Identity Cloud passwords are always stored in encrypted format. Even administrators are unable to access a user’s password.
Yes, it’s that secure.
And did we mention client reputation, an Akamai capability that rates the “risk score” of a client based on previous history associated with the client’s IP address (i.e., “This IP address has been used before in known phishing attacks. We should require two-factor authentication for this user.”)? Well, we should have mention risk-based authentication and client reputation, because those are two more ways to help keep your site – and your users’ personal data – safe and secure.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription.
Do you have to use this feature? No. If you think two-factor authentication would be overkill for your users and for the type of user information you store, then here’s a suggestion: don’t enable two-factor authentication. It’s as simple as that. Don’t want to require your users to use complex passwords? Then don’t require them. It’s entirely your decision.
Recommended reading: Two-factor authentication (2FA); Introduction to trusted devices; Introduction to unique password enforcement; 2FA and RBA Getting Started Guide
Overview video: Multi-factor authentication: Email (video); Multi-factor authentication: SMS; Trust a device (video)
Customize the user experience
By default, when you first access Hosted Login you’ll see a sign-in screen with the Akamai logo at the top, a sign-in screen that also uses Akamai colors, an Akamai favicon, Akamai terminology and fonts, etc., etc. Admittedly, it’s possible that you don’t actually want an Akamai-themed and branded sign-on screen. And that’s fine: Identity Cloud makes it a snap to change the logo or the favicon or the wording used on the screen. If you have even a modest understanding of CSS it’s possible to create an entirely different sign-in experience:

They sky, as they say, is the limit.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription.
Do you have to use this feature? Technically, no: if you want to have your screens emblazoned with an Akamai logo that’s up to you. But note that changing the logo means modifying a single configuration setting: no coding required.
Recommended reading: Customize Hosted Login
Overview video: Screen customization (video)
Enable users to securely view and manage their personal data,
If you manage an app or a website, you’re no doubt familiar with the European Union’s GDPR (General Data Protection Regulation) and similar initiatives designed to protect user privacy and give users ownership over the data you collect and maintain about them. With that in mind, you’ll be happy to hear that the Identity Cloud is not only compliant with the GDPR, but also with ISO 27001; ISO 27019; AICPA’s Trust Services Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy; with the – well, you get the idea. Users have a mechanism for requesting copies of their user data, and they also have a mechanism for requesting that their accounts be deleted and their user data removed from the system altogether.
On top of that, Identity Cloud makes it easy to customize the data that you collect and maintain. For example, by default the Identity Cloud’s entity types (i.e., user account databases) don’t have a way to track a user’s favorite color or their lucky number. You say you have a compelling reason to request that information from users? Then request it: entity types can be modified to store any data you want them to store. And, as alluded to previously, Identity Cloud screens can easily be modified to request that data.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription.
Do you have to use this feature? Organizations have the option of choosing the data that they will or will not maintain for their users. (With a couple of exceptions: for example, if users are logging on with a username and password you’ll have to, at a minimum, store their username and password.)
Recommended reading: Default user schema
Overview video: Profile data management (video); Hosted Login end-user experience (video)
Keep a near-real time watch on your site
SIEM (Security Information and Event Management) is the standard way to monitor, aggregate, and analyze the events that occur on your websites and in your apps. Among other things, the use of SIEM events and a dedicated SIEM analysis tool can do such things as keep a running tally of user password resets. Yes, users legitimately reset their passwords from time-to-time. However, an unexpectedly large number of password resets, all occurring at the exact same time, is often a sign of a security breach. Again, just to name one example, a SIEM tool can alert you anytime the number of reset passwords starts to exceed the expected number of resets. In turn that provides you with a heads-up that there’s, potentially at least, something a bit nefarious taking place.
See Identity Cloud SIEM events for information about the event types available to you.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription.
Do you have to use this feature? No. We should also add that Identity Cloud provides only the “raw” SIEM events, text files that look similar to this:
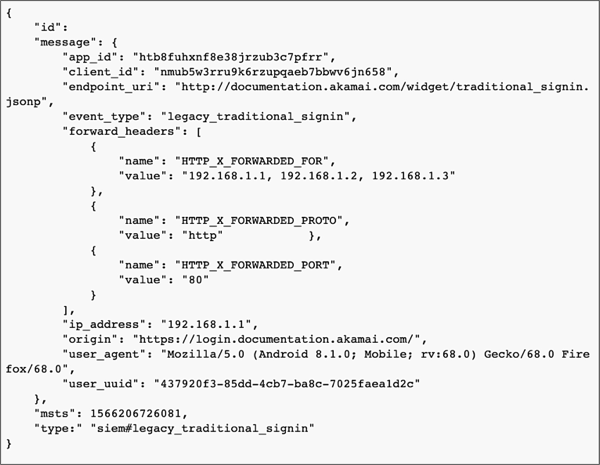
To take full advantage of SIEM you might want to invest in a full-fledged SIEM analysis took such as Splunk or IBM QRadar.
Recommended reading: Introduction to SIEM event delivery
Overview video: SIEM event delivery (video)
Keep tabs on user events of particular interest
There are bound to be certain user events that are of special interest to your organization. For example, suppose you’re having a special event in which a reward of some kind is sent to anyone who creates a new account on your site. In a case like that, you’d like notification any time someone creates an account, the better to add them to the list of people to be sent the reward. Similarly, you might like to be notified any time a user clicks the Request My Data button in their user profile; that way you can quickly gather up and send the requested data to that user. Knowing how many users go to their user profile and change their middle names might not be too terribly interesting to you; knowing how many users go to their user profile and change their user consents from Allow to Deny might be a different story.
Again, you get the idea.
Identity Cloud’s Webhooks v3 service provides a way for you to receive near-real time notifications each time a specified user event occurs. Do you need to know each time a user changes their middle name? That’s fine: then configure a Webhooks subscription that watches for the change-your-middle-name event. And what if you don’t care whether or not users change their middle name? That’s also fine: in that case, don’t configure a Webhooks subscription that watches for the change-your-middle-name event. Like most Identity Cloud features, whatever you do (or don’t do) with Webhooks v3 is entirely up to you.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription.
Do you have to use this feature? No. And thanks to Webhooks filtering, even if you do choose to use Webhooks v3, you can easily pick and choose which events you want to be notified of and which events you don’t want to be notified of.
Recommended reading: Introduction to Webhooks v3; Introduction to Webhook event filters
Overview video: Webhooks v3; Webhooks v3 Getting Started Guide
Review and analyze website statistics
Webhooks v3 is a fantastic way to be notified each time a specified user event occurs. Did a user just create a user account? Bang! Here’s your notification. Did another user just create a user account? Bang! Here’s another notification. Did someone else just create a third user account? Bang! Here’s a third notification.
Etc., etc.
There’s nothing wrong with being notified each time an event occurs. However, if that was the only way you got data you might risk missing the forest for the trees: after all, instead of knowing that user accounts were created at 11:01 AM and 11:02 AM and 11:03 AM, you might be interested in knowing how many accounts have been created this month, period. And you might be interested in knowing how that compares to the number of accounts t created last month. And you might be interested in knowing, based on current trends, how many new accounts might be created next month.
Again, you get the idea.
To provide a different perspective on your app or website statistics, and to help you analyze and make sense of those statistics, Identity Cloud customers can use Customer Insights, the Identity Cloud’s primary data analysis tool. By default, the Identity Cloud ships with a number of “dashboards” that provide you with data similar to this:
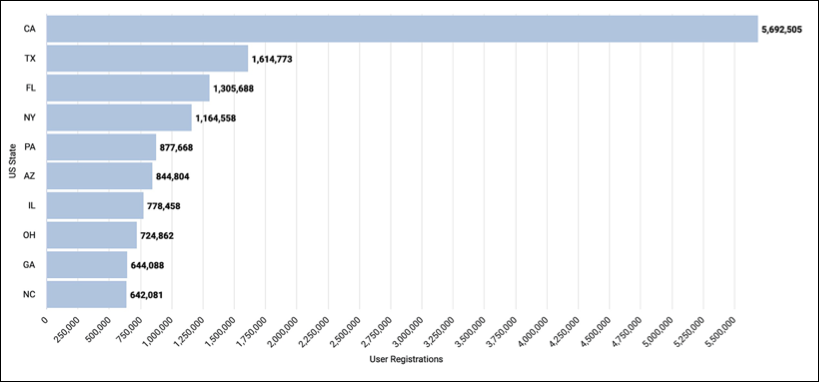
As usual, these reports are fully customizable. Don’t like bar charts? That’s OK; maybe a pie chart would be better:
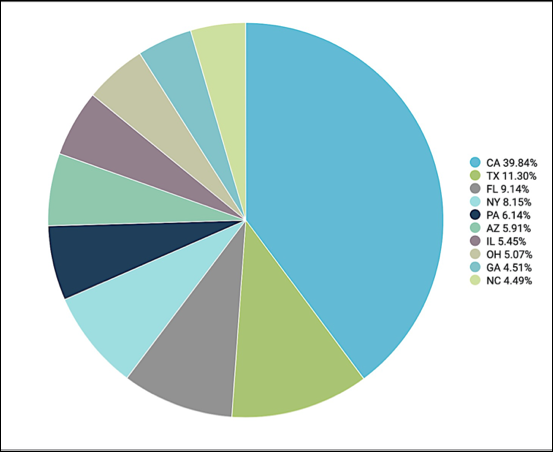
Or a word cloud:
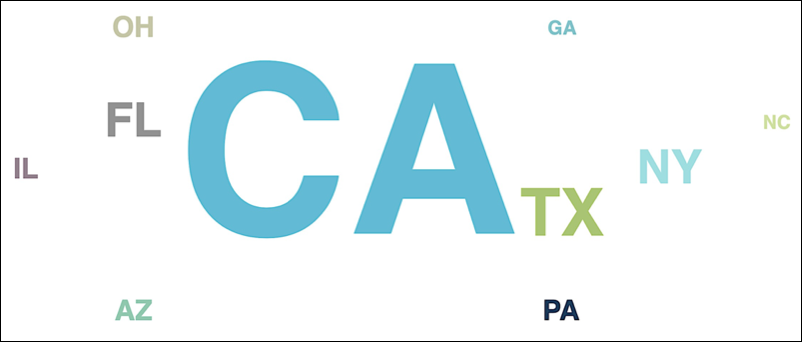
Or maybe just an old-fashioned table:
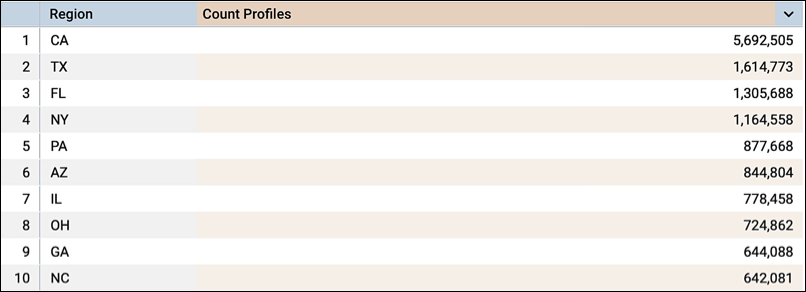
And what if the default set of dashboards doesn’t include the data you’re most interested in? You got it: Customer Insights lets you create your own dashboards and your own charts and graphs.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription.
Do you have to use this feature? No. But once you’ve seen how just powerful Customer Insights really is, we’re not sure why you wouldn’t want to use it.
Recommended reading: Introduction to Customer Insights
Overview video: Customer Insights
Share data with other platforms
Although we’re somewhat-biased, we believe that Identity Cloud is the best Customer Information and Access Management software on the market. On the other hand, we’re the first to admit that it’s not necessarily the best Customer Relations Manager (CRM) software or the best video game software on the market. And that’s OK, because our Integration Bus feature makes it possible for you to share your user data with, say, your CRM software. For example, Integration Bus can be configured so that each time a new user account is created on your Identity Cloud website that information is copied to Salesforce Marketing Cloud:
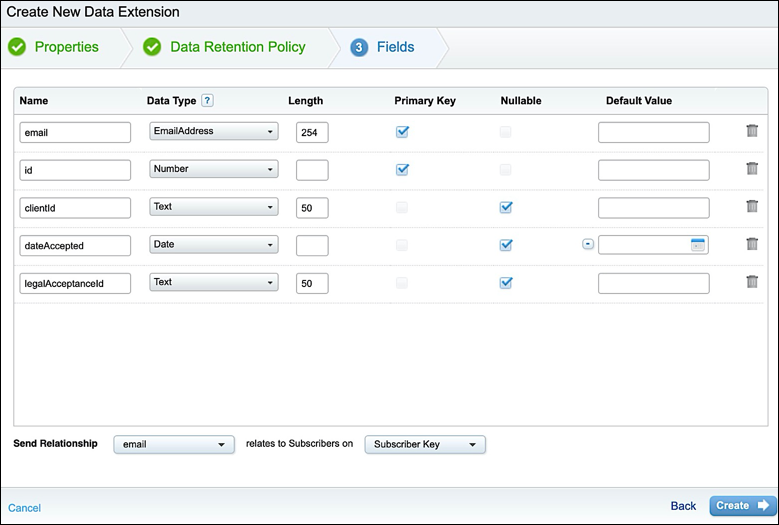
And what if that data changes somewhere along the line? You’re way ahead of us: yes, user data can be synchronized from the Identity Cloud to Salesforce and vice-versa.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription
Do you have to use this feature? No.
Recommended reading: Integration Bus Getting Started Guide
Seamlessly switch over to Identity Cloud
Identity Cloud is definitely tempting, but if you’re already using a CIAM platform you might be concerned about those hundreds of thousands (maybe even millions) of user accounts you’ve already collected. Are you really supposed to make all those users create brand-new Identity Cloud accounts?
To cut to the chase, here’s your answer: no. Instead, and by using Identity Cloud’s data migration service, you can migrate existing accounts from your current platform to the Identity Cloud:
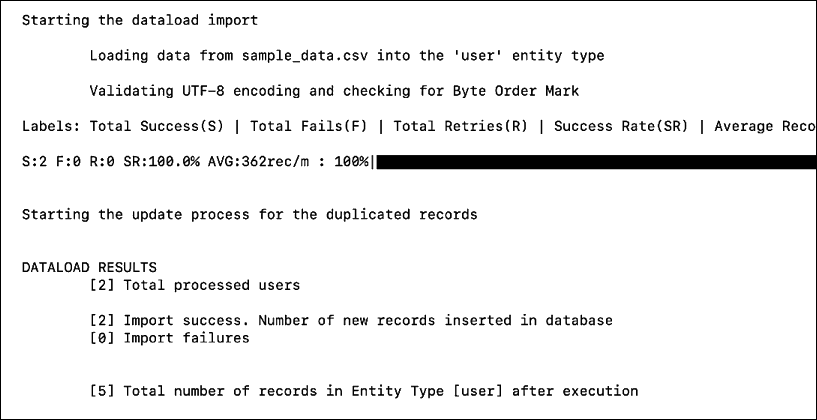
And this migration includes not only the account itself, but also all the data associated with that account, including the user’s password. If you’ve been thinking, “I’d switch to Identity Cloud, but it would be too hard to move all my user accounts off my current platform,” all we can say is this: you’re going to have to think much harder to come up with a reason not to make the switch.
Do all Identity Cloud customers have access to this feature? Yes, this is included as part of your Identity Cloud subscription
Do you have to use this feature? No. And even if you do want to migrate from another CIAM vendor that doesn’t mean that you have to use data migration: if you’d prefer, Akamai will do the data migration for you.
Recommended reading: Self-service data migration
Updated about 1 month ago
