The custom origin (publicly trusted certificate)
Follow this workflow to add a custom origin—"Your origin"—server to your property.
Before you begin: Understand the request flow
This is optional, but it's recommended. Take a minute to familiarize yourself with the flow of a request involving the Akamai network.
1. Meet some prerequisites
Before you can define a custom origin in your property, you need to get your origin server set up.
This workflow uses a publicly trusted certificate authority for an origin server. It's a simpler process to implement and the certificate is recognized by the Akamai certificate store. You can also customize this process by using a custom certificate authority, or pinning an exact certificate.
The policy for managing Akamai's list of trusted authorities and the actual list that is updated regularly can be found in our GitHub repository.
2. Prepare your edge certificate
The first phase of a request flow involves the end user contacting Akamai edge servers. To secure this connection with HTTPS, you'll need to prepare your edge certificate.
If you need to use the custom certificate method, you'll need to wait until it completes provisioning before you can set up your Property Manager property. You'll receive an email once it's ready.
3. Set up your property
If you haven't yet, perform these operations to initially set up your property in Property Manager:
- Create a brand new property
- Define a secure property hostname (for delivery via HTTPS)
- Define property variables (optional)
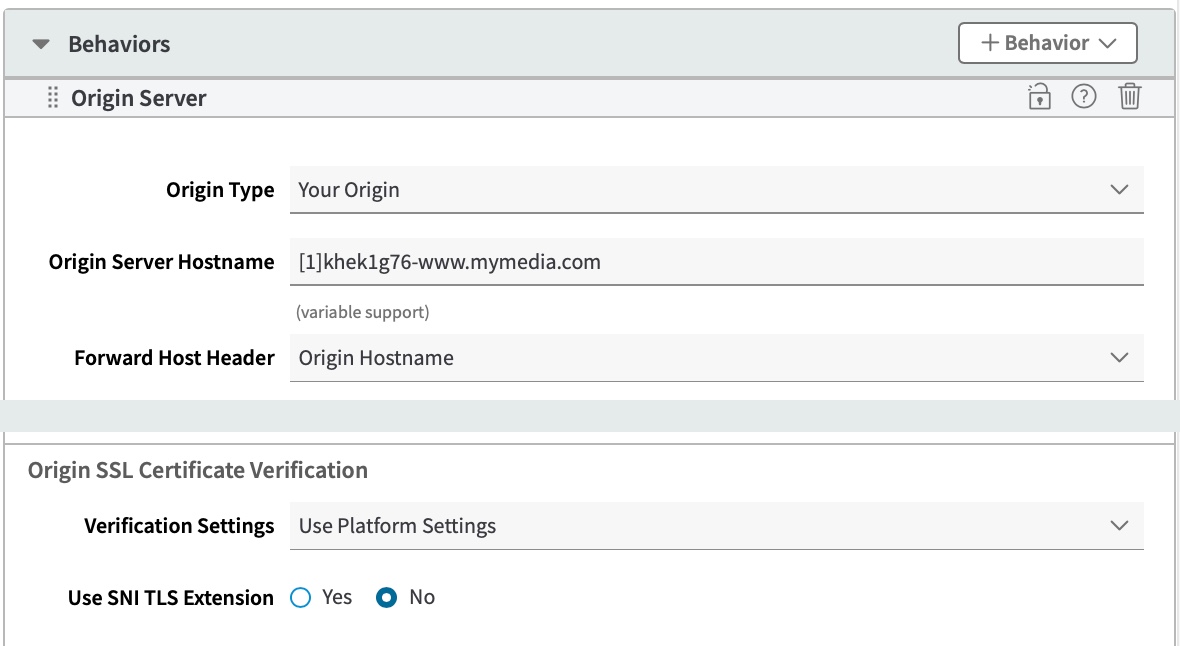
4. Set up the Origin Server behavior
Now you need to configure Property Configuration Settings to set up your custom origin.
-
Ensure the Default Rule is selected.
-
Set Origin Type to Your Origin.
-
Enter the Origin Server Hostname that you established when you set up your origin server.
Variable supportThis field supports variable expression syntax. Typing "{{" in the option field triggers a list of objects to select. Additional details on this support are available by mousing over this option in the UI. Also see Variables overview.
-
Select the appropriate Forward Host Header. The selected header must be what's set as the Common Name (CN) or Subject Alternate Name (SAN) in your origin certificate.
-
Set the following options, as desired:
-
In Origin SSL Certificate Verification setting, define the following:
-
Verification Settings. Select Platform Settings. When you set up and applied your publicly trusted origin certificate, you used a certificate authority that's known to be trusted by the Akamai Certificate Store. Selecting Platform Settings simply tells edge servers to trust any certificate signed by the authorities listed in the Akamai Certificate Store. There's no customization required with this workflow.
-
SNI TLS Extension. Set this to No for this workflow. It only applies if your origin server has been configured to host multiple Standard/Enhanced TLS certificates to support multiple sites. If this is the case, set this to Yes. The Server Name Indication (SNI) header will be sent in the SSL request to the origin. The SNI header value that's sent is the same as the header you've selected for Forward Host Header.
-
- Leave the Ports options at their defaults unless your origin server uses different ports. The standard port for HTTPS traffic is 443.
Are you using Ion?An Ion property contains specific rules that you can configure to optimize end-user access and use of your origin server:
Set up Origin Connectivity. Within the Accelerate delivery rule, this sub-rule lets you optimize the connection between edge and origin.
Configure the Origin Offload rule. Here, you'll use several sub-rules to control caching content at the edge and in an end user's browser.
Updated 3 months ago
