How activation works
Akamai CDN has two networks: staging and production. Activation pushes updates across the staging (testing) or production (customer-facing) networks for property versions.
During activation, Akamai deploys changes in phases to minimize risk and ensure the most relevant edge servers for active traffic receive updates quickly.
Activation times can vary depending on the state of your property. See Exceptions.
For instructions on how to activate a property version, see Activate your property.
Activation is also available through Property Manager API (PAPI).
Phases of activation
Staging
Activating property versions on the staging network is a faster process than activating on the production network. There are a few key differences as to why activations roll out faster on the staging network:
- The staging network is smaller than production.
- The staging network doesn’t serve end user traffic.
- Activations don’t require phased rollout.
When activating a property version on the staging network, Akamai monitors to make sure all staging servers have received the updated version configuration so that you can test as needed in a safe, non-end user-facing environment.
Activations on the staging network usually finish within 3 minutes.
Production
Akamai uses a phased approach to push your property’s configuration changes through the production network to ensure complete safety and reliability.
Phase 1: Activate for live traffic
The first phase of activation updates live traffic servers:
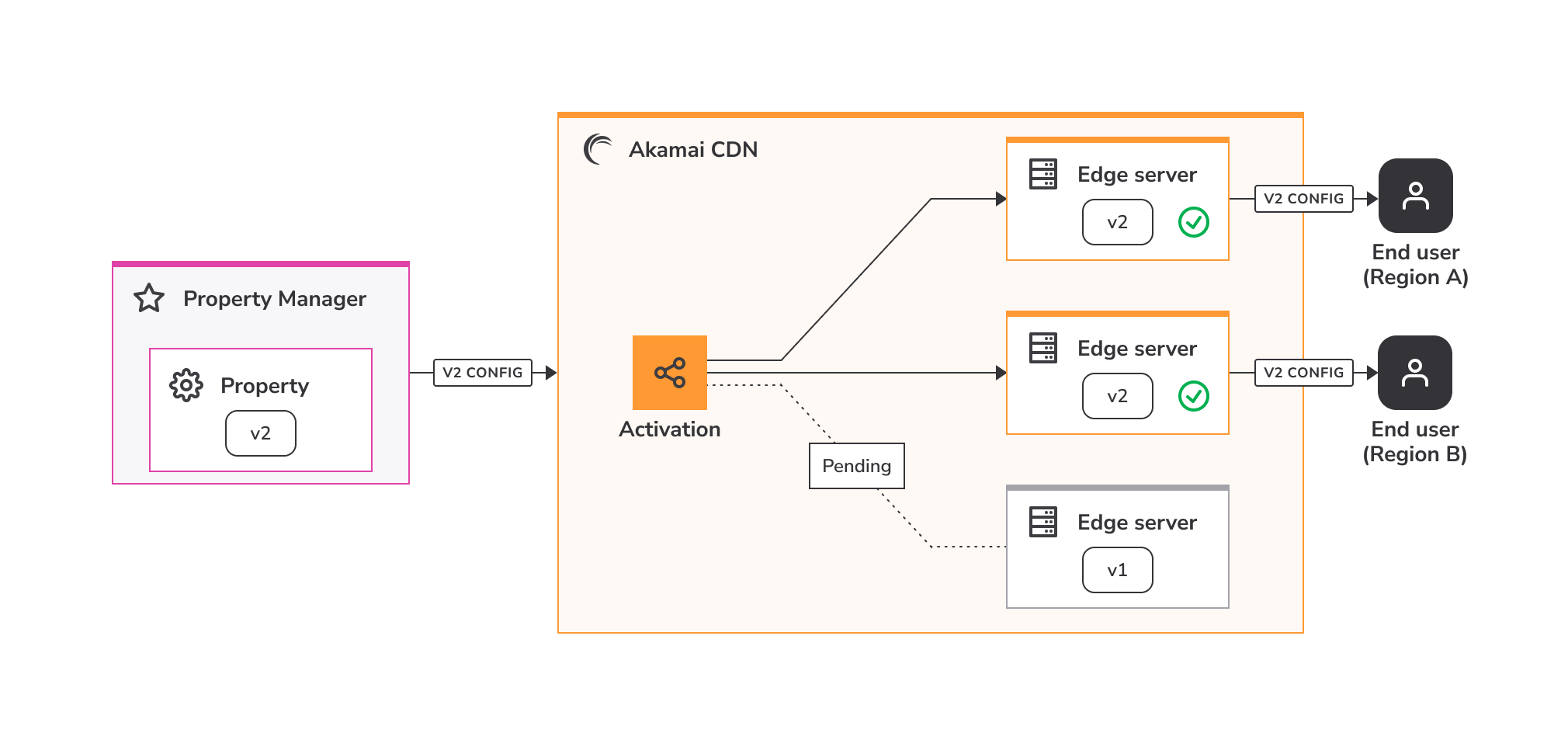
- When you activate a property on the production network, Akamai identifies and targets updates to edge servers actively serving traffic for your application or service. These servers are usually within the specific geographical location that’s close to the requesting clients.
- After the live traffic servers have been identified, Akamai updates them with the new property configuration. Depending on how many edge servers are being used to serve live traffic, Akamai may first update a smaller group of servers so they can be monitored before rolling out to the remaining servers. Akamai focuses on the edge servers serving live traffic early in the activation process so that you can see and test the effects of your activation as soon as possible.
- Akamai monitors the updated servers to make sure no problems like increased error rates, software issues, or server overload are present. At this point, you can also check your own metrics for any inconsistencies. If any issues are detected, either you or Akamai can cancel the activation, and changes are rolled back.
Phase 1 of activation generally completes in under 4 minutes, but can be influenced by a variety of factors, including the number of live traffic servers being updated. You can see the status of this phase using the tracking progress bar in Property Manager, and a successful activation message is displayed once Akamai has pushed your updates to live traffic servers.
End users mapped to new edge locations within a few minutes of this phase may still reach Akamai servers with the previous property configuration. This could happen if edge servers in specific geolocations aren’t serving significant end user traffic at the start of the activation, and new end users connect to those edge servers before they’ve been updated.
Phase 2: Continued rollout
The second phase of activation updates the rest of the Akamai network:
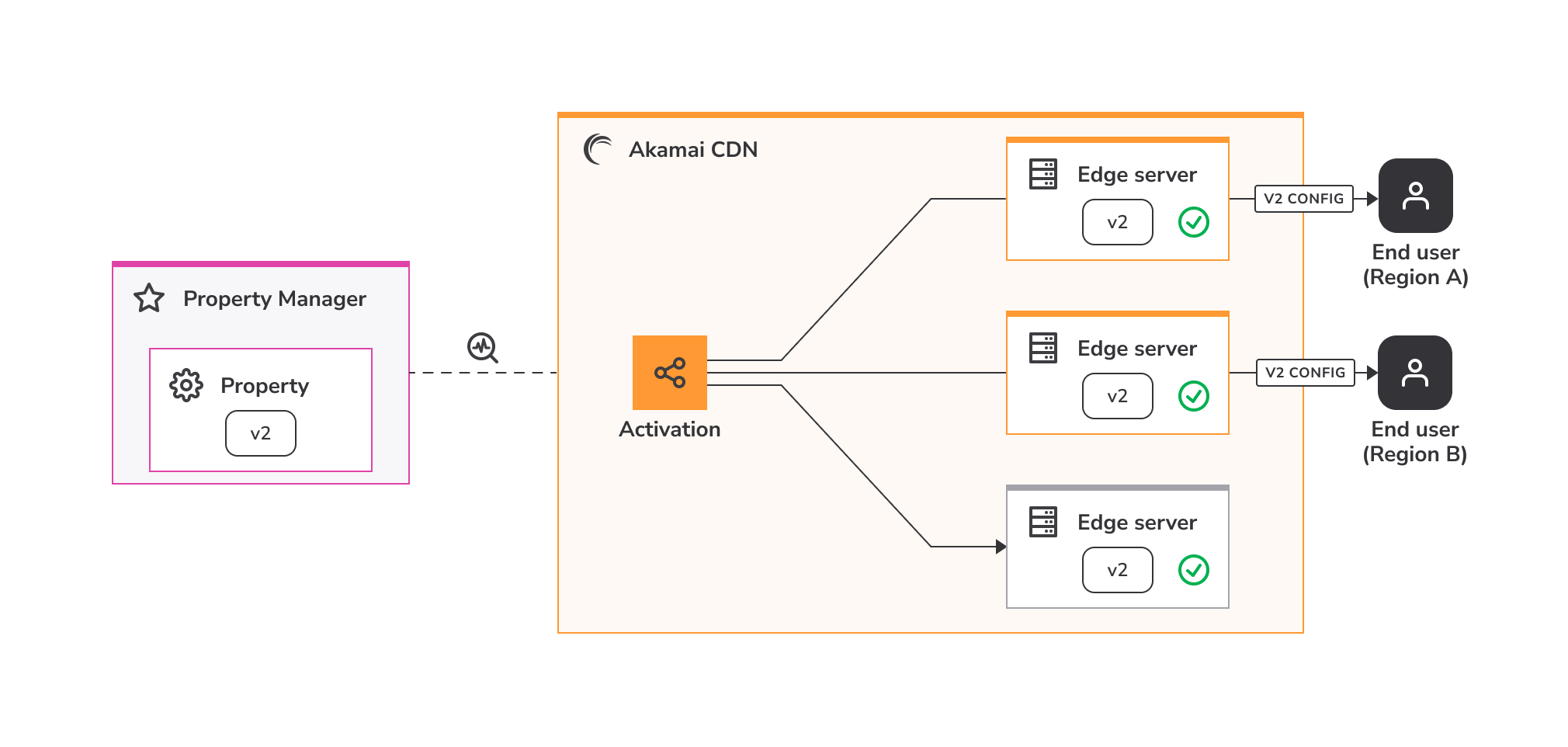
- After the first phase completes, live end-users are being served traffic through the latest configuration. You can start validating your changes while Akamai gradually pushes out the update to the rest of the production network. Akamai monitors the remaining edge servers as they’re updated to ensure your new property version is safely functioning and available to end users globally.
- Property Manager displays a Pending - Full Rollout status in your property’s Activation History during this phase. If the system detects a problem that could affect your site, Akamai automatically cancels the activation and lets you know. You also have the ability to manually cancel your activation at this time.
- At this point, you can continue validating your changes while the activation remains locked for editing. New activations can start once this phase is fully complete. If there are any issues post-activation, there is a 60 minute window where you can quickly revert to your most recent active property version using the Fast Fallback feature.
The total activation process takes up to 15 minutes on the production network, and Property Manager displays an Active status in your property’s Activation History when it’s complete.
What does Akamai monitor?
During the activation, Akamai monitors updated servers to make sure the proposed configuration changes are safe. Akamai looks for things like:
- Increased error rates. See HTTP error rate limit.
- Changes, or any negative impacts, to status codes.
- Unexpected behaviors like server unavailability or reboots.
- Any other negative impacts to the overall performance that may result in customer-facing disruptions.
Exceptions
Activations can take up to 60 minutes for the following scenarios:
-
Property versions where more than 10 property hostnames at a time are added, removed, or reconfigured.
-
Custom or advanced property configurations that require intervention by Akamai.
-
Property configurations that involve migrating hostnames from legacy Configuration Manager.
Time estimates
The following table is a summary of the different types of activation actions and phases, and their estimated completion times.
| Action or phase | Time estimate |
|---|---|
| Staging network activation | 2-3 minutes |
| Production network: Live traffic activation* | 3-4 minutes (90% of activations) Up to 7 minutes (99% of activations) |
| Production network: Full rollout | Up to 15 minutes |
| Fast Fallback | 2-3 minutes |
| Fast Fallback window | 60 minutes after full rollout |
| Exceptions | Up to 60 minutes |
*Determined by the number of live traffic servers being updated.
Cancel an activation
You can cancel an activation on both staging and production networks, however cancellation availability may vary:
-
If your property doesn't fall under exceptions, you may cancel an activation at any time before it's complete. This results in the last active version being restored on Akamai's network.
-
If your property does fall under exceptions, there is a limited time in which you may cancel the activation. The Cancel button becomes inactive after a certain threshold of servers have been updated, after which the activation continues for the new property version. If you cancel the activation, the process does not continue, and the currently active version remains active.
To cancel an activation:
- Navigate to your property’s Activate tab in Property Manager.
- Look for the Cancel button while activation is still underway.
- Click Cancel.
- When the confirmation window pops up, confirm by clicking Yes, cancel.
Fast Fallback
Akamai recognizes your need to continuously test and validate multiple changes in your environment. After activation is 100% complete, you have a 60 minute window to revert, or fall back, the configuration to your most recent active property version using the Fast Fallback feature.
Fast Fallback works by reactivating the last active property version before your activation was initiated. Similar to activating a property on the production network, the Fast Fallback process occurs in two phases, including initial roll out and monitoring for live traffic servers, and continued rollout to the rest of the network.
Fast Fallback can accommodate more live traffic servers in a shorter amount of time and finishes faster than a standard activation. The entire process generally completes within a few minutes depending on how many edge servers need to be rolled back.
For example: You just activated and went live with version 4 of your property configuration on Akamai's network. Next, you activate version 5 to include some caching updates. After the testing period is complete, and within a few minutes of version 5 being fully activated on production, you notice something looks off with your metrics. You know that the last change in your environment was the version 5 configuration update. Using Fast Fallback, you quickly revert to your last active property configuration (version 4). This lets you determine whether the issue is with your newest configuration update or something else that requires further troubleshooting.
To use Fast Fallback:
- Navigate to your property’s Activate tab in Property Manager within 60 minutes of the activation process completing.
- Click the Fast Fallback to last active version button.
If you miss the 60 minute window and want to revert to a previously active version, return to the Property Details page, select the active version to which you want to revert, and activate it.
Fast Fallback considerations
Make note of these limitations for Fast Fallback:
-
You need to successfully activate at least one property version before using Fast Fallback, since it requires a previous version for which to revert.
-
You can’t use Fast Fallback for property versions that fall under exceptions.
Edit an active property
You can’t edit a property that’s already active on either the staging or production networks. If you need to edit a currently active property, create a new version.
Once you create a new property version, you can edit, save, review, test, and submit the changes through activation to replace the configuration that’s currently active. See Properties for more information on how to use versions for editing active properties.
If you have previously activated two or more versions of a Property Manager configuration, you can view an XML diff by selecting the Diff Against vN link in the Currently Active row. This is a more advanced functionality for users who are familiar with the XML code that is used to implement the configuration.
HTTP error rate limit
For properties that don't fall under exceptions, Akamai applies an error rate limit. If the traffic for the property that’s being activated reaches the thresholds for HTTP errors, Akamai may automatically cancel the activation.
When does the limit apply?
The error rate limit check looks for extreme changes in errors and traffic and is meant to protect your site while minimizing false positives.
Akamai currently applies the rate limit and can cancel the activation if:
-
The ratio of successful
2xxhits to total hits drops by 90%. -
The ratio of
2xxand3xxhits to total hits drops by 90%. -
The ratio of
4xxand5xxerrors to total hits increases by more than 10 times.
If the activation of a new version leads to a significant increase in 4xx and 5xx errors or a decrease in 2xx and 3xx responses, Akamai automatically rolls back to the previously active property version and notifies you about the incident.
When does the limit not apply?
Akamai does not apply the error rate limit if your site or application has fewer than 1000 hits per second on average. Lower levels of traffic are more prone to higher variations and more likely to produce false positives resulting in the activation being cancelled.
Turn off the error rate limit
If your activation is cancelled due to the error rate limit being reached, try to fix any issues in your property version configuration, and activate it again. Alternatively, you can turn this feature off when activating your property if you are expecting changes in errors or traffic:
- Navigate to your property version’s Activate tab in Property Manager.
- After selecting Activate v# on Production, look for the Cancel Activation if Error Rate Increases option.
- Deselect the option.
- Click Activate v# on Production to continue with the activation.
Don't deactivate this additional safety feature unless you expect a significant increase in the error rate and are prepared for it.
Consider these examples where you may expect increased error rates:
-
Turning on Web Application Firewall (WAF) to block potentially malicious traffic.
-
Adding geo-blocking to prevent access by some countries, states, or provinces.
-
Adding any other type of access control settings that result in denying access to some subset of traffic like Referrer Checking.
Updated about 1 month ago
