Origin Characteristics & Download Delivery
This behavior lets you set characteristics for your origin server to optimize access to it.
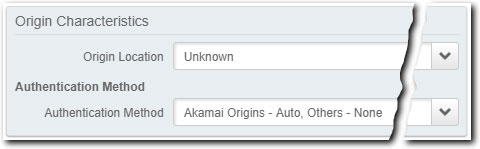
Origin Location
Select the appropriate location of the origin server, based on its Origin Type:
-
NetStorage. Set this to Unknown.
-
Your Own Origin. Select the geographical location of your origin server to optimize access to it. Do this to implement what we consider "use case-based provisioning" for this behavior. If you're not sure about your server location, select Unknown.
Authentication Method
Select the appropriate authentication method for use:
| Method | Description | Additional options |
|---|---|---|
| Akamai Origins - Auto, Others - None | This is the default and applies if your origin server doesn't have any external authentication requirements, or if you're using NetStorage as your origin. | N/A |
| Interoperability Google Cloud Platform | Select this if you're authenticating with Google Cloud Storage (GCS) as your origin. Support is based on the GCS V4 signing process. Once selected, configure the additional options that are revealed. |
|
| Amazon Web Services | Select this if you're authenticating with Amazon Web Services (AWS) cloud provider as your origin. Support is based on the AWS signature version 4 signing process. Once selected, configure the additional options that are revealed. |
|
Additional considerations for GCS or AWS
Consider these points when using GCS or AWS as your cloud origin provider:
-
You can use Cloud Access Manager. Use it to streamline the client authentication process. See Cloud Access Manager & Download Delivery for complete details.
-
You can check your authentication details in the file you saved when creating your HMAC key. If you didn’t download the file, or if you lost it, you may need to delete the existing HMAC key and add a new one. See Managing HMAC keys in GCS or Managing Access Keys (console) in AWS for details.
-
You may be eligible to streamline client authentication by using Cloud Access Manager. See Client access keys for cloud provider-based origins for details.
-
Use a property with an akamaized hostname. This lets you either retrieve objects from the origin, or for read-only bucket operations. This is because we're currently limited to storing cloud provider access keys in cleartext. This doesn't carry the level of protection you might expect for the transmission of personally identifiable information (PII).
-
Consider using two separate sets of cloud provider access keys. Dedicate one to GET operations and another to POST, PUT, or DELETE operations. For all GET operations, set them up to use a property via Property Manager; for POST, PUT, and DELETE operations, you should use the APIs or SDKs offered by the associated cloud provider.
-
Regularly rotate the cloud provider access keys. This reduces the likelihood of unauthorized diversion of confidential information.
-
Only the "Authorization" header is supported (AWS, only). If you're using query string parameters with this authentication, each query parameter in the incoming client request must be sorted alphabetically, and URL encoded.
Tiered Distribution is preset as a “best practice”
It's automatically enabled in the background of the Origin Characteristic behavior. This lets Download Delivery retrieve your cached content from another mid-tier of servers that are closer to your origin server, rather than directly from your origin server. For cached content, the feature has significant advantages:
- Reduction in demand for bandwidth at the Origin Server, which is often positive in itself and necessary to upscale applications.
- Improved performance from the reduced time it takes for the product to retrieve content. Tiered Distribution parent servers are generally located close to the production servers that use them.
Disable Tiered Distribution
If you need to disable it, you can add Tiered Distribution as an optional behavior in the same rule and set it to "Off".
Tiered Distribution can't be used with Cloud WrapperIf you've added the Cloud Wrapper service to your Download Delivery property, you need to disable Tiered Distribution.
Origin Characteristics and Mixed Mode
Origin Characteristics is a "use case-based" behavior that's automatically included in the Default Rule and used to optimize delivery for all requests. However, with Mixed Mode Configuration for DD, you can include it in another rule and apply different match criteria to have separate requests use different origin characteristics optimizations. For more details, see Mixed Mode & Download Delivery.
Updated 3 months ago
